Accueil
De Wiki livre Netizenship
Télécharger ce livre en PDF ?
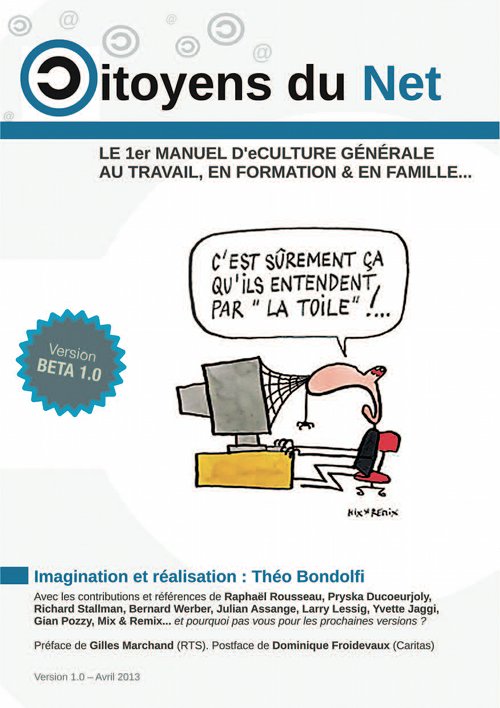
Dernière version en date : version Beta 1.0 (Avril 2013 - PDF, 37.08 Mo), cliquez sur l'image ci-dessous.
Contribuer ? Découvrez d'abord la Communauté des contributeurs et l'Aide générale wiki.
- Table des matières du livre citoyens du net, en version wiki pour vos contributions.
- Notre application des Tags pour documenter le livre citoyens du net, en version collaborative.
- Racines de l'économie numérique, une adaptation du chapitre 5 pour montrer ses liens avec l'Economie Sociale.
- Netizen Economy, une adaptation du livre en anglais, résumant CDN sous l'angle économie et citoyenneté
- Netizenship Polish edition, une adaptation du livre en polonais
- CoWaBoo, une plateforme qui facilite la gestion des signets (bookmarks)
- Credit Commons, A platform of intercommunity transactions - Une plateforme des transactions intracommunautaires (blockchain)
- Wikinomics Badges, openbadges scenarios et activités liées avec la Wikinomie
- 5 STPDE,The socio-technical properties of digital environments
- ESIC,European Social Innovation Competition
- eCulture Project, Présentation du projet Interreg "eCulture"
- Stage 2017, STAGE MULTIMÉDIA SOLIDAIRE ET MARKETING ÉTHIQUE 2017
Couverture